Network Design & Implementation
Overview
A reliable IT environment begins with structured, well-planned network architecture. Network Design & Implementation focuses on building stable, secure, and scalable infrastructure that supports daily operations without bottlenecks, instability, or recurring faults.
Poorly designed networks often lead to slow performance, dropped connections, security gaps, and unpredictable downtime. We eliminate these risks by planning capacity correctly, segmenting traffic, implementing proper routing and switching configurations, and ensuring physical infrastructure supports long-term growth.
From small offices to multi-floor commercial sites, we design networks that support VoIP systems, cloud applications, CCTV systems, file servers, remote workers, and wireless access all operating together without congestion or security compromise.

Architecture Planning: We assess your operational needs, user count, device density, internet capacity, and future expansion plans. This ensures your network backbone, switching layer, and access layer are properly structured from the start.
Network Segmentation: VLAN configuration separates critical systems (servers, CCTV, accounting, guest Wi-Fi) to improve performance and reduce security exposure. Proper segmentation prevents internal congestion and limits risk if one device is compromised.
Redundancy & Stability: Where required, we implement failover internet links, redundant switching paths, and proper UPS-backed network cabinets to reduce downtime during power or connectivity disruptions.
Security Foundations: Firewall configuration, controlled port access, secure remote access setup (VPN), and hardened router settings are implemented to reduce unauthorized access risks.
Performance Optimization: Bandwidth allocation, Quality of Service (QoS) for VoIP or priority systems, and wireless channel planning ensure stable performance even during peak usage.
Testing & Documentation: Every deployment includes structured testing (latency, throughput, failover validation) and clear documentation of IP schemes, device configurations, and rack layouts for future maintenance.



We develop structured network blueprints that align with business operations and anticipated growth.
- Logical and physical topology design
- IP addressing schemes and subnet planning
- Bandwidth and throughput analysis
- Redundancy and failover planning
- Security zone mapping (VLAN segmentation)
- Cloud and hybrid infrastructure integration planning
- Implementation roadmap with phased deployment
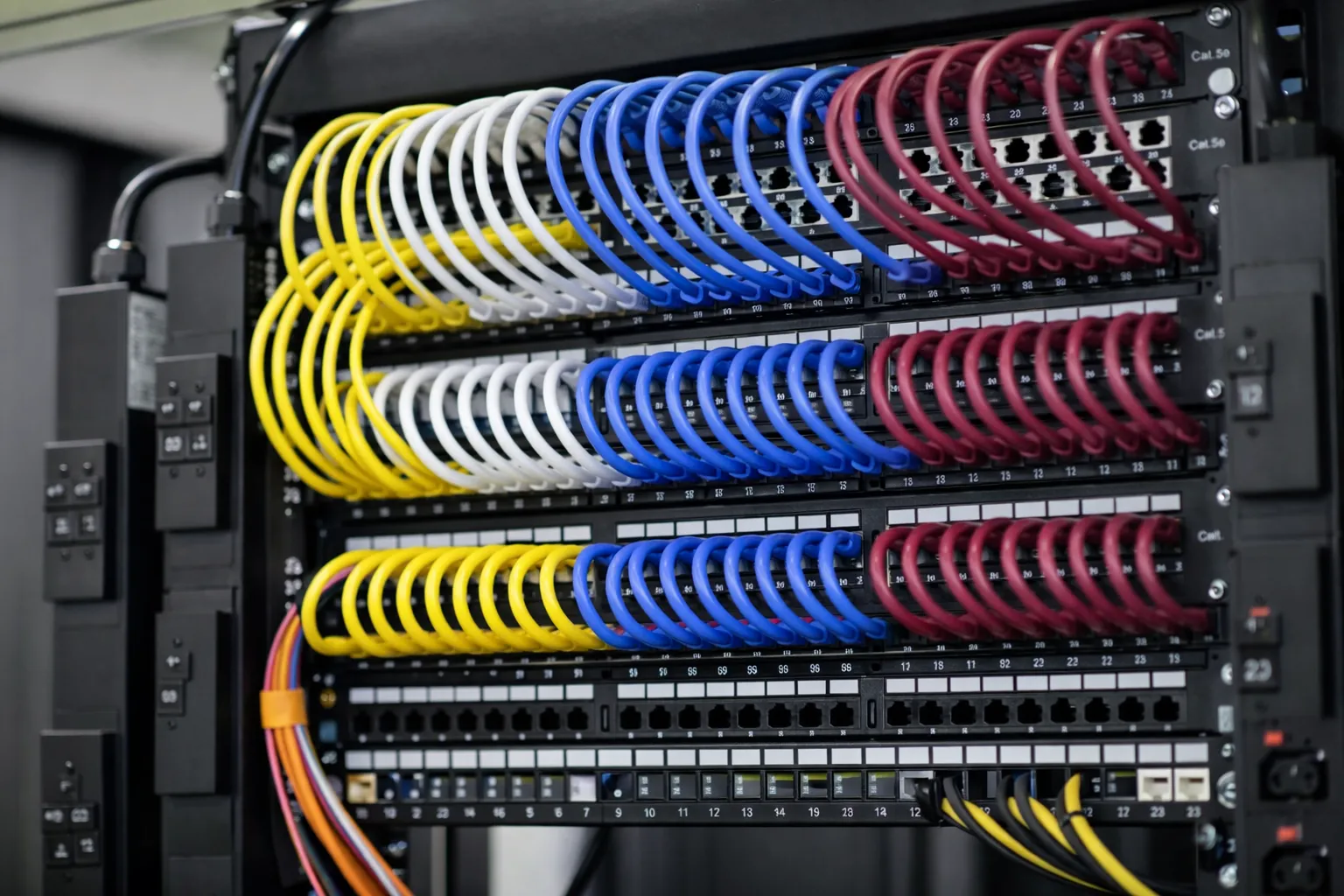
Clean, labeled, and tested cabling forms the physical backbone of stable networking.
- CAT6 / CAT6A installation
- Fiber backbone deployment where required
- Patch panel termination and labeling
- Server rack organization and airflow planning
- Cable certification and testing reports
- PoE planning for wireless and CCTV devices
- Future capacity allowance planning
Equipment is configured according to best practices to ensure long-term reliability.
- Router and firewall hardening
- Managed switch configuration (VLAN, trunking)
- Wireless access point deployment and tuning
- QoS setup for VoIP and priority traffic
- Secure VPN configuration for remote staff
- Internet failover and load balancing setup
- Post-installation performance validation
Who This Service Is For
Network Design & Implementation supports organizations that require stable, secure, and scalable connectivity:
New Office Deployments
Businesses establishing infrastructure from the ground up.
Growing Organizations
Companies expanding beyond unmanaged switches and basic routers.
Security-Focused Environments
Organizations requiring segmented and firewall-protected systems.
High-Performance Workloads
Operations relying on cloud services, VoIP, CCTV, and remote access.
Build a Stable Network Foundation
Design your network properly from the start structured, secure, and scalable for long-term performance.
Start Network Planning →Wireless Network Solutions
Overview
Wireless networks are no longer a convenience they are core infrastructure. Staff mobility, cloud systems, VoIP handsets, POS devices, CCTV integrations, scanners, and guest access all depend on stable and properly engineered Wi-Fi coverage.
Poor wireless design results in dead zones, dropped calls, unstable remote sessions, buffering, and constant user complaints. These issues are usually caused by incorrect access point placement, unmanaged interference, bandwidth congestion, or security misconfiguration.
We design structured, business-grade wireless networks that prioritize coverage consistency, controlled access, roaming stability, and long-term performance not just signal strength.

Coverage Engineering: We perform structured site analysis to determine correct access point density, placement height, wall/material interference, and device load expectations. The goal is even coverage not overlapping signal chaos.
Capacity Planning: Modern networks must support laptops, smartphones, smart TVs, IoT devices, scanners, and CCTV streams simultaneously. We calculate concurrent device loads and configure access points accordingly.
Roaming Stability: Proper configuration allows users to move throughout a building without dropped calls or session interruptions critical for VoIP and warehouse scanning operations.
Traffic Segmentation: Guest Wi-Fi, internal staff access, CCTV devices, and IoT systems are separated using VLANs and controlled routing to improve performance and reduce internal security risks.
Interference Management: Channel planning, transmit power tuning, and environmental scanning help minimize congestion caused by neighboring networks or industrial equipment.
Centralized Management: Where required, controller-based or cloud-managed systems are deployed to simplify monitoring, updates, and troubleshooting across single or multiple sites.



Wireless planning ensures correct density, balanced coverage, and stable roaming.
- Onsite wireless site surveys
- Access point density calculations
- Channel overlap and interference analysis
- Coverage heat mapping (where required)
- Capacity planning for concurrent users
- Wireless network segmentation planning
- Future expansion and scalability mapping
Installation follows structured networking standards to ensure long-term reliability.
- Ceiling/wall-mounted access point installation
- PoE switch configuration
- SSID planning and VLAN mapping
- Controller or cloud management setup
- Roaming optimization configuration
- Throughput and latency validation testing
- Post-deployment performance verification
Wireless access must be secure, segmented, and monitored especially in internet-facing environments.
- WPA3 / WPA2-Enterprise configuration
- 802.1X authentication setup
- Guest network isolation
- Rogue access point detection
- Bandwidth control policies
- Access control lists (ACLs)
- Periodic security review and password policy enforcement
Who This Service Is For
Wireless Network Solutions support organizations that depend on consistent mobility and connectivity:
Office Environments
Businesses requiring reliable employee and guest Wi-Fi.
Retail & Hospitality
Operations relying on POS systems, guest access, and mobile devices.
Education & Healthcare
High-density environments requiring controlled, stable wireless access.
Warehouses & Industrial Sites
Facilities using scanners, mobile terminals, and roaming devices.
Strengthen Your Wireless Infrastructure
Implement structured wireless networking that delivers stable coverage, secure access, and long-term performance.
Plan Wireless Deployment →Network Security
Overview
Network security is not a single device or “one setting” it is a structured approach that controls who can access your network, what they can reach, and how threats are detected and contained. Most security incidents in small and medium environments start with simple issues: weak passwords, open remote access, outdated firmware, unmanaged Wi-Fi, or staff devices connecting without proper controls.
We implement practical, layered security for business networks: secure firewall policies, controlled remote access, segmentation for critical systems (servers, POS, CCTV, guest Wi-Fi), and monitoring practices that help detect suspicious activity early. The goal is operational security reducing real risk without breaking your day-to-day work.
Security also includes verification. A network can “look fine” while still being exposed for example: remote viewing ports left open, default passwords on a recorder, overly broad admin permissions, or no separation between guest Wi-Fi and office systems. We identify and fix these gaps with clear documentation and sensible recommendations.

Threat Reduction in Plain Terms: We limit exposure by closing unnecessary ports, hardening routers/firewalls, enforcing strong authentication, and separating systems so an infection or compromise in one area does not spread across your whole network.
Secure-by-Design Networks: We align firewall rules, VLANs, and access permissions with how your business actually operates accounting systems stay protected, guest networks stay isolated, and critical devices like servers and CCTV recorders are restricted to only what they need.
Remote Access Done Properly: Instead of risky “open access” setups, we implement secure VPN access with correct permissions. This is safer for remote staff and also for systems like CCTV remote viewing.
Ongoing Security Hygiene: We review policies, firmware, and user access as your environment changes. Many breaches happen months after a network change that quietly introduced a gap regular review prevents that.



Firewalls are most effective when configured around real operations: what services you use, who needs access, and what should never be exposed. We harden the perimeter and build rules that protect the network without breaking productivity.
- Router/firewall hardening (disable risky services, secure management access)
- Inbound/outbound rule control (least-privilege policy)
- Intrusion prevention and threat blocking (where supported)
- Web filtering and malicious domain blocking (where required)
- Port exposure reviews (CCTV remote viewing, RDP, web servers)
- Firewall change logs and configuration backups
- Regular policy review to remove old/unused rules
VPN access provides a safer alternative to exposing internal systems directly to the internet. We configure encrypted tunnels with correct permissions, device controls, and access boundaries.
- Remote access VPN for staff and administrators
- Site-to-site VPN for branch connectivity
- Role-based VPN access (users only reach what they need)
- Multi-factor authentication setup (where supported)
- Device onboarding and secure client configuration
- Split tunneling vs full tunneling guidance (based on risk)
- VPN testing, documentation, and recovery procedures
We implement access control that prevents unauthorized devices and limits internal movement. This reduces risk from stolen passwords, infected laptops, or staff devices connecting to sensitive areas.
- 802.1X authentication (where supported)
- Guest Wi-Fi isolation and captive portal options
- Device segmentation for CCTV, POS, printers, and IoT
- Role-based access and admin permission controls
- BYOD policies (staff phones/laptops) and safe access design
- MAC-based controls for legacy devices (where needed)
- Access reviews and cleanup (remove unused accounts/devices)
Who This Service Is For
Network Security supports organizations that rely on internet-connected operations and need controlled access:
Regulated & Audit-Driven
Organizations needing stronger controls, logs, and data protection practices.
Remote Workforce
Teams that access company systems from home, travel, or multiple locations.
Businesses Using CCTV / POS
Sites where remote viewing, recorders, and payment devices must be protected and segmented.
Growing Networks
Organizations expanding users/devices and needing security that scales with them.
Secure Your Network Properly
Reduce exposure, control access, and implement secure remote connectivity with practical network security design and setup.
Request Security Assessment →Network Management & Monitoring
Overview
Most network problems don’t fail loudly they degrade quietly: internet links get saturated, Wi-Fi channels get noisy, switches start dropping packets, DNS becomes unreliable, or a router reboots due to heat or power instability. Monitoring turns these “slow failures” into visible alerts and trends so issues are fixed before they become downtime.
Our Network Management & Monitoring service provides structured oversight of your routers, switches, access points, links, and key services. We track availability, performance, and configuration changes, then respond with practical corrective actions: isolate the cause, stabilize the environment, and document what changed.
The focus is operational clarity: you know what’s online, what’s struggling, what caused the alert, what was done to resolve it, and what should be planned for next whether that’s adjusting QoS, upgrading a link, replacing a failing power supply, or segmenting traffic more effectively.

Real-Time Visibility: We monitor device uptime, link quality, interface errors, bandwidth usage, Wi-Fi health, and critical service availability. This helps detect issues like failing ports, overloaded links, unstable wireless, or misconfigured DNS before users report “the internet is slow.”
Proactive Maintenance: Alerts are paired with action: verify root cause, apply safe changes, confirm stability after the fix, and record outcomes. This reduces repeat issues and avoids “restart and hope” troubleshooting.
Change Awareness: Many outages are caused by silent changes ISP modem swaps, router updates, firewall rule edits, or new devices added without planning. We track configuration baselines and highlight meaningful changes to reduce unexpected breakage.
Reporting & Trends: Health reports summarize uptime, recurring faults, peak usage times, and capacity constraints. This supports smarter budgeting and planning (e.g., when to upgrade internet, add access points, or segment CCTV/guest traffic).



Monitoring is structured around what matters: uptime, performance, and evidence of faults. Alerts are tuned to reduce noise and highlight real impact, with escalation paths for critical issues.
- Device uptime and service availability monitoring (routers, switches, APs)
- Internet link monitoring (latency, packet loss, jitter, outages)
- Bandwidth utilization and peak usage tracking
- Interface/port error monitoring (CRC, drops, flaps)
- Wi-Fi health monitoring (AP status, client load, roaming issues)
- Automated alerting with severity levels and escalation
- Incident logging with root-cause notes and corrective actions
- Historical dashboards for trending and planning
Optimization is based on measurements, not assumptions. We use trends and metrics to apply targeted changes that improve user experience and protect critical traffic (VoIP, POS, CCTV, cloud apps).
- QoS configuration for VoIP and priority traffic
- Traffic shaping and bandwidth allocation policies
- Wi-Fi performance tuning (channels, power, client steering)
- VLAN segmentation refinement (guest, staff, CCTV, IoT)
- Router/firewall performance tuning and rule cleanup
- Capacity planning (when to add APs, upgrade links, expand switching)
- Application impact checks (cloud apps, Teams/Zoom, POS systems)
Documentation reduces downtime because troubleshooting becomes faster and repeatable. It also helps with handovers, audits, and future upgrades because you’re not rebuilding knowledge from scratch.
- Network topology diagrams (logical and physical)
- IP addressing plans and device inventories
- SSID/VLAN mapping and access control notes
- Configuration backups and baseline snapshots
- Change logs (what changed, when, why)
- Standard operating procedures (restart, failover, recovery)
- Disaster recovery notes for routers, firewalls, and switches
Who This Service Is For
Network Management & Monitoring is valuable where connectivity affects operations and support calls are costly:
Business-Critical Operations
Organizations where outages stop work, sales, or customer service.
Growing Networks
Businesses adding users, devices, Wi-Fi, CCTV, and cloud services.
Multi-Site Operations
Teams needing consistent standards and remote visibility across locations.
Compliance & Accountability
Environments that need documented operations, access, and change records.
Get Clear Visibility & Faster Support
Improve stability and response times with structured monitoring, practical optimization, and clear network documentation.
Request Monitoring Setup →Business Network Solutions
Overview
Business networks must do more than “connect devices.” They must support accounting systems, cloud applications, VoIP phones, CCTV infrastructure, file sharing, printers, wireless users, remote staff, and guest access all operating reliably at the same time.
Many commercial environments struggle with networks that were expanded without proper planning. Over time, additional routers, unmanaged switches, exposed Wi-Fi, and inconsistent security policies create instability and risk. Business Network Solutions address this by building structured, scalable infrastructure aligned with real operational requirements.
We design complete commercial networking environments from office floor cabling to multi-site secure connectivity ensuring systems remain stable, secure, and ready for future growth.

Operational Alignment: Network architecture is structured around how your business operates separating staff, guest, accounting, CCTV, POS, and IoT systems to improve both performance and security.
Reliability & Stability: Proper switching, firewall policies, and bandwidth allocation ensure cloud platforms, VoIP calls, and critical applications perform consistently during peak usage.
Scalable Growth: Infrastructure is designed with expansion in mind additional users, new departments, new branches, or increased internet capacity can be integrated without redesigning the entire network.
Standardized Management: Structured configuration, documentation, and centralized visibility reduce long-term support costs and simplify troubleshooting.



Complete office networking designed around business workflow and security requirements.
- Commercial network architecture planning
- Structured cabling and rack installation
- Router, firewall, and switch configuration
- Wireless network deployment and segmentation
- VoIP readiness and QoS configuration
- CCTV and IoT network isolation
- Secure remote access setup
- Full testing and documentation
Connecting multiple business locations securely and efficiently while maintaining centralized visibility and control.
- Site-to-site VPN implementation
- Secure WAN connectivity planning
- Centralized firewall policy management
- Unified VLAN and segmentation standards
- Redundant internet failover planning
- Inter-branch application optimization
- Remote monitoring and support integration
Structured networking to ensure stable and secure access to cloud services such as Microsoft 365, cloud accounting, backup platforms, and hosted applications.
- Cloud traffic prioritization (QoS)
- Firewall security alignment with cloud services
- Hybrid network design (local + cloud systems)
- Secure VPN integration with cloud platforms
- Bandwidth assessment for cloud workloads
- Cloud migration network readiness checks
Who This Service Is For
Business Network Solutions support commercial organizations that rely on stable and scalable infrastructure:
Small to Medium Businesses
Companies requiring dependable networking for daily operations.
Growing Organizations
Businesses expanding users, departments, or physical locations.
Cloud-Integrated Businesses
Companies relying heavily on cloud applications and remote access.
Multi-Site Enterprises
Organizations needing secure inter-branch connectivity and centralized management.
Strengthen Your Business Infrastructure
Implement structured networking that supports your operations today and scales with your growth tomorrow.
Plan Business Network →Network Troubleshooting
Overview
Network problems are often reported in vague ways “the Wi-Fi is slow”, “emails won’t send”, “the POS is offline”, or “Teams keeps dropping.” The root cause can sit anywhere in the chain: ISP instability, DNS failure, IP conflicts, failing switch ports, overloaded routers, incorrect firewall rules, wireless interference, cabling faults, or power fluctuations.
Our Network Troubleshooting service follows a structured process to isolate the fault quickly and restore stability without guesswork. We troubleshoot layer-by-layer (physical, switching, routing, services, and applications), confirm evidence of the failure point, then apply the correct fix and verify normal operation afterward.
The focus is not only to “bring the internet back” but to prevent repeat incidents by documenting findings, cleaning up risky configurations, and recommending practical improvements where needed.

Evidence-Based Diagnostics: We use targeted tests to confirm what is failing: link status, interface errors, IP/DHCP/DNS behavior, gateway reachability, latency and packet loss, and service availability so the fix addresses the real cause, not symptoms.
Fast Isolation: We narrow down whether the issue is local (Wi-Fi/AP, switch, cabling), edge-related (router/firewall), or external (ISP/WAN), reducing downtime and unnecessary device replacements.
Controlled Fixes & Verification: Changes are applied carefully and tested afterward: confirm internet stability, verify internal access, check cloud apps, validate VPN connectivity, and ensure critical systems (VoIP/POS/CCTV) operate normally.
Service Records: Each incident includes findings, the action taken, and prevention notes useful for recurring faults, handovers, audits, and future upgrades.



We test systematically across the network stack to isolate the exact failure point and confirm root cause.
- Physical checks (cabling, ports, link negotiation, power/PoE)
- Switch diagnostics (port errors, loops, VLAN mismatch)
- Router/firewall checks (NAT, routes, rule conflicts)
- IP conflict, DHCP scope, and gateway validation
- DNS resolution checks (internal + public DNS behavior)
- Latency, packet loss, and jitter measurements
- Baseline comparison (what changed vs what used to work)
- Root-cause findings with corrective action notes
We resolve failures affecting internet access, internal network communication, branch connectivity, and remote users.
- ISP/WAN outage isolation and escalation support
- Router/gateway failures and configuration recovery
- VPN connectivity issues (site-to-site and remote access)
- Wi-Fi dropouts, roaming failures, and signal interference
- Switch port failures and patching problems
- Routing issues and subnet misconfiguration fixes
- CCTV remote viewing and cloud access interruptions
Performance issues are investigated using traffic measurements and behavior analysis to identify the bottleneck.
- Bandwidth usage analysis and peak-time investigation
- Latency and jitter troubleshooting (VoIP/Teams/Zoom impact)
- Congestion detection (uplinks, Wi-Fi, WAN saturation)
- QoS validation and correction
- Wireless channel/power tuning and client load balancing
- Application path checks (cloud apps, hosted systems, POS)
- Hardware capacity checks (router CPU/RAM, switch uplinks)
Who This Service Is For
Network Troubleshooting supports organizations that need fast recovery and long-term stability:
Recurring Problems
Businesses dealing with repeat disconnections, outages, or unstable Wi-Fi.
Performance Complaints
Teams experiencing slow cloud apps, lag, buffering, or VoIP call drops.
Outage Response
Organizations needing urgent restoration when operations are disrupted.
Complex Environments
Sites with VLANs, VPNs, CCTV, multiple APs, or multi-site connectivity.
Fix the Root Cause Not the Symptoms
Restore connectivity and improve stability with structured troubleshooting, verified fixes, and documented outcomes.
Request Troubleshooting →Network Upgrades & Migration
Overview
Network upgrades should improve reliability and security not create downtime. Many businesses run on aging routers, unmanaged switches, outdated Wi-Fi, and “patched together” cabling that worked when the network was small but becomes unstable as more devices, cloud services, CCTV, and remote access are added.
Our Network Upgrades & Migration service modernizes your infrastructure in a controlled way: assess what you have, identify real constraints (speed, coverage, congestion, security gaps), then migrate configurations and services with clear rollback plans and verified testing. The result is a smoother transition with minimal disruption to operations.
Upgrades may include replacing end-of-life equipment, improving switching capacity, moving to managed Wi-Fi, introducing segmentation (VLANs), tightening firewall policies, improving redundancy, or expanding the network to support new departments, branches, or higher bandwidth usage.

Planning & Risk Control: We map your current network, document configurations, and identify dependencies (internet, VoIP, POS, CCTV, servers, Wi-Fi). Each change includes a risk review, a rollback method, and a cutover approach that fits your operating hours.
Configuration Migration: Firewall rules, VLANs, DHCP/DNS settings, VPNs, and Wi-Fi SSIDs are migrated carefully with cleanups where needed. This avoids carrying forward old insecure or conflicting configurations into new equipment.
Phased Implementation: Where possible, upgrades are done in stages to keep operations running install and test new equipment, migrate segments gradually, then decommission old hardware once stability is confirmed.
Verification & Documentation: After cutover we validate performance (speed, latency, roaming), confirm remote access and critical services, and deliver updated diagrams, IP plans, and configuration backups.



Technology upgrades improve stability and performance when implemented with correct capacity planning and configuration. We upgrade based on actual needs user/device load, service requirements, and future growth.
- Switching upgrades (uplinks, PoE capacity, managed switching)
- Wi-Fi upgrades (better coverage planning, roaming stability, higher capacity)
- Firewall upgrades (policy control, VPN improvements, safer remote access)
- Network segmentation upgrades (VLANs for staff/guest/CCTV/POS/IoT)
- WAN improvements (failover links, load balancing where required)
- Cloud readiness upgrades (QoS, DNS stability, routing optimization)
- Security hardening during upgrades (remove defaults, close risky exposure)
Aging devices often fail gradually random reboots, overheating, unstable ports, or slow throughput. We replace equipment in a way that preserves existing services and reduces downtime.
- End-of-life router/firewall replacement with rule migration
- Switch replacement (PoE, uplink upgrades, VLAN migration)
- Access point replacement with SSID continuity and roaming tuning
- Configuration backups and baseline snapshots before changes
- Cutover scheduling aligned with business hours
- Post-migration validation (internet, VPN, Wi-Fi, services)
- Asset records and safe decommissioning guidance
Expansion is more than adding a switch. We scale capacity with structure so performance and security remain predictable. This includes addressing cabling, switching, Wi-Fi density, internet capacity, and segmentation.
- New office/department network expansion and structured cabling
- Additional switching and PoE capacity for new devices
- Wi-Fi expansion (additional APs, channel/power planning)
- Branch integration (site-to-site VPN and shared services)
- Bandwidth scaling and ISP upgrade guidance
- Standardized configurations across sites (security + VLAN templates)
- Documentation updates and management/monitoring integration
Who This Service Is For
Network Upgrades & Migration supports organizations that need modernization without operational disruption:
Aging Infrastructure
Networks running on outdated routers, unmanaged switches, or unstable Wi-Fi.
Growth & Expansion
Businesses adding staff, devices, CCTV, cloud apps, or new locations.
Security Modernization
Organizations tightening access control, VPN, segmentation, and firewall policies.
Business Integration
Companies merging networks after relocation, restructuring, or multi-site consolidation.
Upgrade Without Disruption
Modernize your infrastructure with structured planning, phased migration, verified testing, and clear documentation.
Plan Network Upgrade →
Built, Installed & Managed
for Real Business Environments
We design and physically deploy structured business networks from server racks and structured cabling to enterprise Wi-Fi access points and secured firewalls. Every installation is planned, labeled, tested, and documented to ensure long-term reliability.
- Structured rack installation and cable management
- CAT6/CAT6A termination and patch panel labeling
- Ceiling-mounted Wi-Fi access point deployment
- Firewall and VPN configuration with secure remote access
On-Site Implementation
Professional deployment with clean, organized infrastructure.
- Rack-mounted routers & switches
- Neatly managed cable runs
- Labeled patch panels
- PoE switching for Wi-Fi & CCTV

Professional Wi-Fi & Structured Cabling Deployment
Reliable wireless starts with correct access point placement and clean cabling. We install ceiling or wall-mounted APs, configure VLAN-based SSIDs, and test signal coverage to eliminate dead zones and interference.
Structured cabling is installed with proper routing, termination, and labeling reducing future troubleshooting time and ensuring the network remains organized as your business grows.
Secured, Monitored & Performance-Tested
After deployment, networks are tested and validated. We confirm internet speed, internal routing, Wi-Fi roaming, VPN access, and cloud application performance.
Firewalls are hardened, unnecessary ports are closed, and secure remote access is configured. Monitoring dashboards provide visibility into uptime, bandwidth usage, and device health.
Designed, deployed, and supported by Encode Tech Solutions.

Request Networking Services Quote
Please complete the form below to request a networking quote, and we'll be in touch. Or you can call us (+27) 081 473 3958 and our specialists will provide the necessary help!